Offshore development centers have funded some of the most impressive engineering scale-ups of the last two decades. They have also quietly derailed product roadmaps, burned through budgets, and ended careers. The difference between those two outcomes rarely comes down to geography or cost. It almost always comes down to how well the risks were understood and managed before the first line of code was written. This guide does not argue for or against offshoring. The economics are real, the talent pools are deep, and for many organizations, building an offshore development center (ODC) is the right call. What it does argue is that the standard advice “communicate often,” “choose a good vendor,” and “align on culture” is too vague to be useful. Risk mitigation at the ODC level requires specifics: which risks, what mechanisms, and how do you know when they are working? Below is a structured breakdown of the seven categories of ODC risk that actually matter, followed by the mitigation approaches that hold up under real operating conditions.
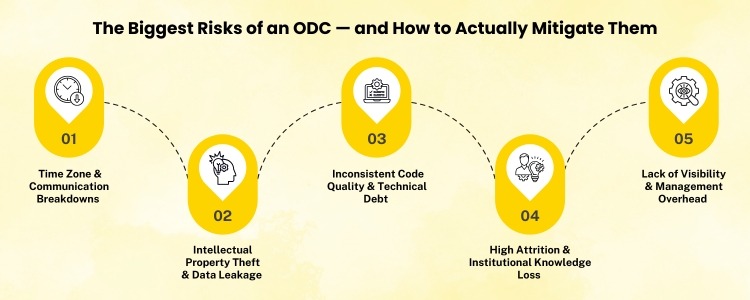
Time zone differences are blamed for most offshore communication failures. They are a contributing factor, but rarely the root cause. The actual problem is usually one of the following: ambiguous requirements that sound clear in English to a native speaker but carry none of the implicit context, a feedback loop too slow to catch misinterpretation before it compounds, or a team culture where raising a concern feels riskier than staying quiet and guessing. A misunderstood requirement that takes two days to surface costs one day to fix. The same misunderstanding discovered after a two-week sprint costs the entire sprint. How to mitigate it
IP risk is the category most companies underestimate until they are actually exposed. Offshoring means your source code, your customer data architecture, your proprietary algorithms, and sometimes your unreleased product roadmap are being accessed from outside your home jurisdiction. The legal protections available in your home country often do not extend in the same form to offshore locations. Some countries have weaker IP enforcement frameworks; others have frameworks that are strong on paper but slow in practice. Neither is acceptable if you are dealing with genuinely proprietary technology. How to mitigate it
A well-established pattern in ODC engagements: quality is high in the first few months, then gradually degrades. The reasons vary: original strong engineers move on, knowledge transfer is incomplete, technical debt accumulates without the visibility it would have in a co-located team, and standards erode as delivery pressure increases. By the time quality problems are obvious to the business, they are expensive to fix. The insidious thing about quality drift is that it is invisible in sprint velocity metrics. A team can be hitting story point targets while quietly accumulating architectural debt, writing under-tested code, and building features that work but cannot be maintained. How to mitigate it
The headline number in most ODC proposals is the hourly or monthly rate differential between offshore and onshore engineering talent. This number is real but incomplete. Companies that have run ODCs for more than a year consistently find that the true cost is significantly higher than the rate differential implies, once your account for what is not in the initial proposal. Setup and onboarding costs, management overhead, increased documentation requirements, rework costs tied to communication failures, infrastructure for remote access, travel for relationship and governance visits, and the productivity cost of context-switching for onshore team members who are now partially managing an offshore team; these are all real costs, and they are all typically excluded from the vendor’s cost comparison. How to mitigate it
Offshore development markets — particularly in India, Eastern Europe, and Southeast Asia — are competitive. Attrition rates in some markets run 20 to 30 percent annually. In a co-located team, when a strong engineer leaves, their institutional knowledge often stays in the room through colleagues, code reviews, and shared documentation. In an offshore setup, that knowledge can walk out the door and into a competitor’s with very little warning and very little residual. The knowledge concentration risk is compounded when offshore teams work on isolated components with minimal cross-team interaction. A single engineer can quietly become the only person who understands a critical subsystem, and in an offshore context, that is a much harder problem to detect before it becomes a crisis. How to mitigate it
For companies in regulated industries, financial services, healthcare, legal tech, defense, and offshore development creates compliance complexity that goes beyond IP protection. Data residency requirements, audit trail obligations, access control standards, and vendor due diligence processes all become significantly more complicated when engineers are operating from outside the regulatory perimeter. Even for organizations outside regulated industries, security posture is a real risk. Offshore development environments may not meet the same endpoint security, network security, or physical access control standards as your corporate environment, and your security policies may not legally or practically extend to them in the same way. How to mitigate it
Culture misalignment is the ODC risk category most frequently dismissed as soft and least frequently addressed with structural seriousness. But it consistently shows up in post-mortems as a root cause of hard, measurable failures: engineers who built what was asked rather than what was needed because raising a concern felt unsafe; teams that executed instructions without applying judgment because ownership was unclear; offshore leads who did not escalate problems because doing so felt like admitting failure. This is not a criticism of any particular culture. Every culture has strengths and blind spots when it comes to software development practices. The risk is an unexamined difference, where both sides assume they are working from the same implicit norms and discover they are not only after something has gone wrong. How to mitigate it
Each of the seven risk categories above has its own mitigation mechanisms, but they share a common dependency: governance. Without a formal, scheduled, and documented governance process, individual mitigations drift into inconsistency, problems go unescalated until they are crises, and the ODC gradually becomes a disconnected execution arm rather than an integrated part of the engineering organization. Effective ODC governance is not complex. It typically involves a weekly operational rhythm focused on delivery and blockers, a monthly quality and metrics review that looks at code quality, attrition, cost, and security posture, a quarterly strategic review that includes vendor leadership and addresses contractual and relationship-level issues, and a defined escalation path that both sides know and trust. The companies that run ODCs well are not the ones that found a perfect vendor or a perfect location. They are the ones that built a governance structure durable enough to absorb personnel changes, scope changes, and the inevitable friction of cross-geography collaboration and used it consistently, even when things were going well.
None of the mitigations above eliminates ODC risk. They manage it, reduce it, and make it visible enough to respond to. That is the honest framing for any offshore engagement: you are making a calculated bet that the benefits outweigh the managed risks, not that the risks do not exist. The organizations that get into trouble are the ones that decided to offshore and then treated risk management as someone else’s problem, the vendors’, or the team on the ground’s problem. It never is. Ultimately, the accountability for how well an offshore development center performs sits with the organization that built it. Build that accountability from the start, and most of the risks above become manageable. Ignore it, and even a well-selected vendor in an ideal location will eventually surface a problem that could have been avoided.
The most significant offshore development center risks include communication breakdowns, intellectual property exposure, quality drift over time, hidden costs that erode the business case, knowledge concentration from high attrition, security and compliance vulnerabilities, and cultural misalignment. Each risk can be managed with the right governance structure, but none can be ignored at the planning stage. To protect IP in an offshore development center, structure vendor contracts under your home jurisdiction with explicit IP assignment and NDA clauses. Apply the principle of least privilege to code access — no developer should access more of the codebase than their work requires. Where possible, keep core proprietary algorithms onshore and expose only abstracted interfaces to the offshore team. Quality drift in offshore development centers typically results from engineer attrition, incomplete knowledge transfer, and accumulating technical debt that remains invisible in velocity metrics. To prevent it, establish measurable quality benchmarks (test coverage, defect escape rates, code review turnaround), enforce a strict definition-of-done on every sprint, and rotate onshore engineers through the ODC regularly to re-anchor quality standards. Beyond the rate differential, a realistic ODC cost model should include onboarding and setup expenses, management overhead (typically 1–1.5 senior engineers’ time per 10 offshore staff), rework caused by communication gaps, remote access infrastructure, compliance tooling, and travel for governance visits. Most ODCs take 6–12 months to reach operational efficiency, so early-quarter ROI expectations are a common planning mistake. In competitive offshore markets like India, annual attrition can run 20–30%. Mitigate this by treating documentation — architecture decision records, runbooks, onboarding guides — as mandatory deliverables, not optional extras. Rotate engineers across features deliberately so no single person holds exclusive context on a critical component. During vendor reviews, proactively ask about team tenure, time-to-fill metrics, and retention practices. With multifaceted experience in Legal, Advisory, and GCCs, Yashasvi weaves law, business growth, and innovation. He leads a cross-functional team across legal, marketing, and IT to drive compliance and engagement. His interests span Law, M&A, and GCC operations, with 15+ research features in Forbes, ET, and Fortune. A skilled negotiator, he moderates webinars and contributes to policy forums.
A practical guide for technology leaders, CTOs, and product teams evaluating or managing ODCs.
1. Communication Breakdown (And Why It Goes Deeper Than Time Zones)
Intellectual Property Exposure
Quality Drift Over Time
Hidden Costs That Erode the Business Case
Knowledge Concentration and Attrition Risk
Security and Compliance Vulnerabilities
Cultural and Organizational Misalignment
The Governance Infrastructure That Ties It Together
Risk Management Is Not Risk Elimination
frequently asked questions (FAQs)

Yashasvi Rathore
Hey, like this? Why not share it with a buddy?
Related Posts
Recent Blog / Post
- How UK Companies Position Their Offshore Delivery Centers as Thought Leadership Assets April 28, 2026
- Can a Mid-Size Company Benefit from Setting Up a Global Capability Center, or Does It Only Work for Enterprises? April 24, 2026
- How AI Is Changing Talent Acquisition in Offshore Delivery Centers in India April 23, 2026
- What KPIs Should You Use to Measure the Performance of a Shared Service Center? April 22, 2026
- How U.S. Tech Companies Are Shaping India’s Startup Ecosystem Through Offshore Development Centers April 21, 2026
- The Death of Traditional Outsourcing: Why Enterprises Are Choosing Captive ODCs April 20, 2026
- Why Semiconductor & IoT GCCs Are Choosing India Over Southeast Asia April 19, 2026
- Why Global Tech Giants Are Expanding Global Capability Centers in India in 2026 April 16, 2026
- Hidden Costs of Offshore Development Centers That Are Killing Your Budget April 15, 2026
- Risks of Relying on Global Capability Centers During Economic Uncertainty April 14, 2026
- Semiconductor and IoT GCCs: The New Frontier for India’s IT Ecosystem April 14, 2026
- How Build, Operate, and Transfer Supports Digital Transformation April 10, 2026
- Offshore Delivery Center Staffing Model and Structure: A Practical Guide April 9, 2026
- How to Choose the Right Offshore Development Partner: A Strategic Guide for Decision-Makers April 8, 2026
- Why Shared Service Centers Are the Smartest Move US Companies Are Making Right Now April 8, 2026